ShinyHunters Is Holding Rockstar Games Ransom And It All Started With A Third Party Vendor
Watching a multi billion dollar gaming empire get brought to its knees by a compromised analytics tool is the most modern cybersecurity tragedy imaginable.
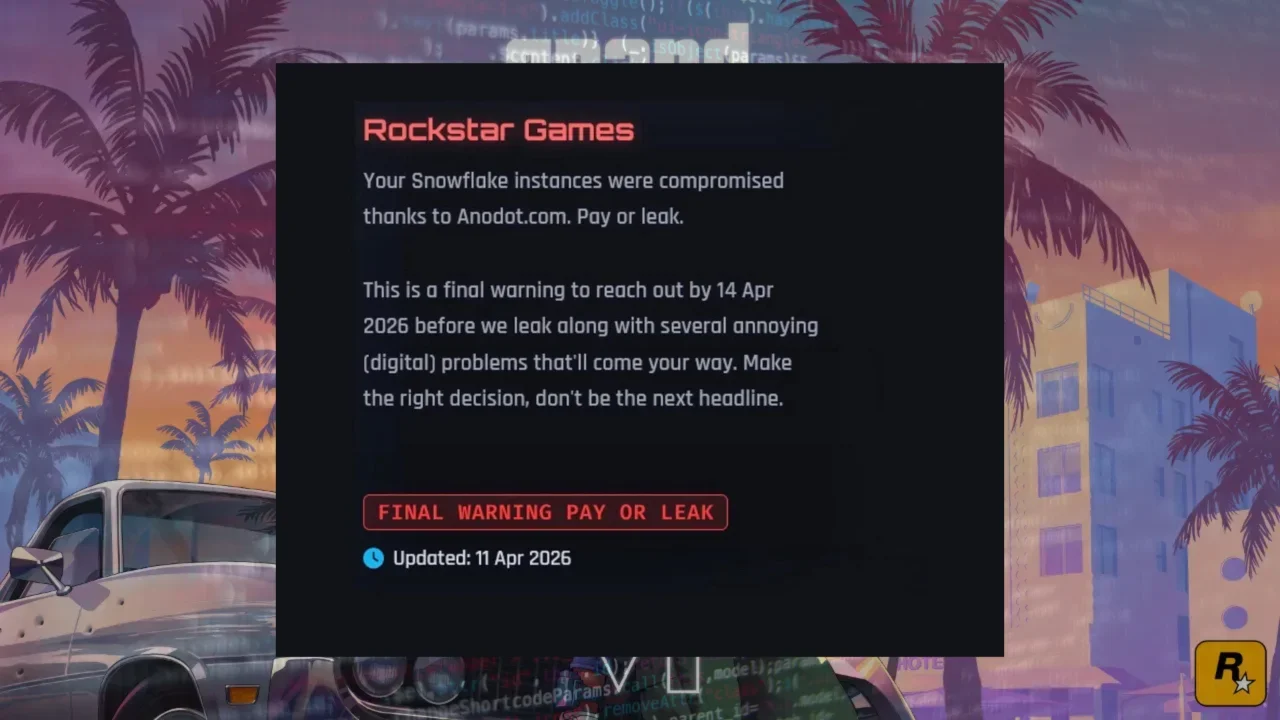
The video game industry is doing this again. I feel like every six months, a massive publisher wakes up to find its most guarded secrets splashed across the dark web. This week, the target is Rockstar Games. A hacking collective known as ShinyHunters has issued a very public, very direct ultimatum. They want a ransom paid by April 14, 2026, or they will leak the company's data. The threat comes packaged with a menacing promise of several annoying digital problems if their demands are ignored.
For anyone sitting at home and looking at the headline, the immediate question is always the same. How does this keep happening? Rockstar is a veritable fortress. They have infinite money, entire floors dedicated to security experts, and the lingering paranoia of previous leaks keeping them awake at night. Yet, a random group of cybercriminals managed to slip through the cracks and hold their data hostage.
The answer is rarely a genius hacker typing furiously to break a firewall like you see in bad Hollywood movies. The truth is much more mundane, deeply frustrating, and entirely reliant on the modern corporate obsession with outsourcing.
The Weakest Link In The Chain
Corporate security is realistically only as strong as the cheapest external vendor allowed into the network.
To understand how Rockstar got compromised, you have to look away from their internal servers and focus on the messy web of cloud integrations they use to keep their business running. ShinyHunters did not kick down the front door of Rockstar headquarters. They found an open window at a completely different company.
The Anodot And Snowflake Connection
The ransom note explicitly points the finger at Anodot, an AI driven platform designed to monitor cloud costs and analytics. Rockstar, like almost every massive corporation on the planet, uses a cloud data warehousing company called Snowflake to store their endless mountains of information. To keep track of their spending and optimize their cloud budget, Rockstar connected Anodot directly to their Snowflake database.
ShinyHunters compromised Anodot first. By breaching that specific third party service, the hackers allegedly managed to pull Rockstar's authentication tokens.
Think of an authentication token like a digital VIP pass. Once you log into a system successfully, the system hands you this pass so you do not have to keep entering your password every five seconds. By stealing those legitimate tokens from Anodot, the hackers essentially walked right past Snowflake's security measures. The cloud servers saw the valid tokens, assumed everything was normal, and handed over access to Rockstar's corporate files. Snowflake itself was not fundamentally cracked. The lock held firm, but the hackers simply stole a spare key from the neighbor.
Human Error Always Wins
When you ask how these groups consistently pull this off, you have to look closely at the human element of IT infrastructure.
Hackers target the people working at these tech companies, not just the raw code. ShinyHunters and their associated groups are notorious for utilizing incredibly aggressive social engineering tactics. They will bypass a firewall by simply calling an employee on the phone, pretending to be from the internal IT department, and claiming they need to immediately update security settings.
The Reality Of Voice Phishing
This tactic is known in the industry as vishing, or voice phishing. The hacker creates a fake corporate login page that looks completely identical to the real internal portal. They convince a stressed, overworked employee to log in to fix a fabricated problem. The exact moment that employee enters their credentials and multi factor authentication codes, the hacker captures the live session token.
There is another incredibly common method called MFA fatigue. A hacker who already has an employee's password will spam their phone with hundreds of login approval requests in the middle of the night. Eventually, the exhausted employee just hits approve so their phone stops buzzing, accidentally letting the hacker right into the network.
It honestly does not matter if a company spends millions on state of the art encryption if an employee can be tricked or annoyed into handing the keys directly to the criminals. Once a threat group has those session tokens, they pivot inside the network, escalating their privileges and silently extracting terabytes of data before anyone realizes there is a rat in the walls.
A History Of Extortion
ShinyHunters is not a ragtag group of kids guessing passwords. They have been running these extortion schemes for years, systematically picking apart the supply chains of massive organizations. They target the connective tissue of the internet. They look for the APIs, the identity management systems, and the analytics software that giant publishers rely on to function.
They know exactly what kind of leverage they need to force a payout. While early reports suggest they might not have access to sensitive personal player data or credit cards, holding Rockstar's corporate contracts, marketing timelines, source code fragments, and financial records hostage is a massive threat.
The April 14 deadline is looming, and it puts Rockstar in a brutal position. If they pay, they fund future attacks. If they refuse, their internal business secrets become public knowledge.